Nesslab provides solutions for Cyber Security and database optimization.
Nesslab’s Solutions Division provides solutions for Cyber Security and Database Optimization.
As one, we support both On-premise and Cloud in the management of privileged account rights as domestic distributors of BeyondTrust, the No.1 company in PAM, which is one area of information protection.
The other is exclusive distribution of Experda’s Data Optimizer products to all customers using MS SQL DB in the Data Optimization field. Get out of the complexity of tuning consulting through manual tasks to ensure business efficiency and productivity through automatic tuning.
1. BeyondTrust
PAM, Private Account Management (PAM) solutions from BeyondTrust in the U.S. are available in three major product lines.
Password & Session Management
Endpoint Privilege Management
Secure Remote Access
- Search and automate account registration : all IT assets and accounts search, identify, and profile
- Session monitoring and management functions : real-time monitoring of session records and rights accounts
- Threat analysis and reporting : Providing threat analysis against vulnerabilities in asset data
- Easy to install : Single interface for easy configuration and management
I. Password & Session Management (Password Safe)
- Complete Platform Coverage : Cloud, IoT, DevOps Endpoints, Windows, Mac, Linux, Unix, and Network Device Protection
- Individual application and command control : Independent deployment architecture model for rapid installation
- Quick installation : Providing threat analysis of asset data vulnerabilities
- Improve security by removing administrator accounts and controlling user accounts and removing administrator accounts (80% or more)
- White Listing, Virus and Ransomware Installation Control
- Securing visibility into managed systems
- Meeting various compliance requirements
II. Endpoint Privilege Management
What is Endpoint? Desktop (window, Mac), and Server (window, Linux, Unix).
[Endpoint Account Rights Management]
- Establishing the SERVICE DESK and Vendors Connection Environment : Building an Access Environment to Maximize Productivity – No VPN required
- Integration of password and session management : Automatically grant permission credentials when users connect to the target system
- Flexible distribution and licensing options : On-Premise, SaaS, Private Cloud, Perpetual, or Subscription license
- Security design : Management URL, user portal, various authentication methods, role-based policy management
III. Secure Remote Access (PRA, Privileged Remote Access)
The BeyondTrust Solution
DISCOVERY • THREAT ANALYTICS • REPORTING • CONNECTORS • CENTRAL POLICY & MANAGEMENT
PRIVILEGED PASSWORD MANAGEMENT
- Discover, manage, audit, and monitor privileged accounts and sessions of all types

ENDPOINT PRIVILEGE MANAGEMENT
- Remove excessive end user privileges on Windows, Mac, Unix, Linux and network devices
SECURE REMOTE ACCESS
- Secure, manage, and audit remote privileged access sessions for vendors, admins and the service desk

Maximize visibility, simplify deployment, automate tasks, improve security and reduce privilege-related risks with the industry’s most innovative and comprehensive privileged access management platform
- ON-PREMISE
- CLOUD
- HYBRID
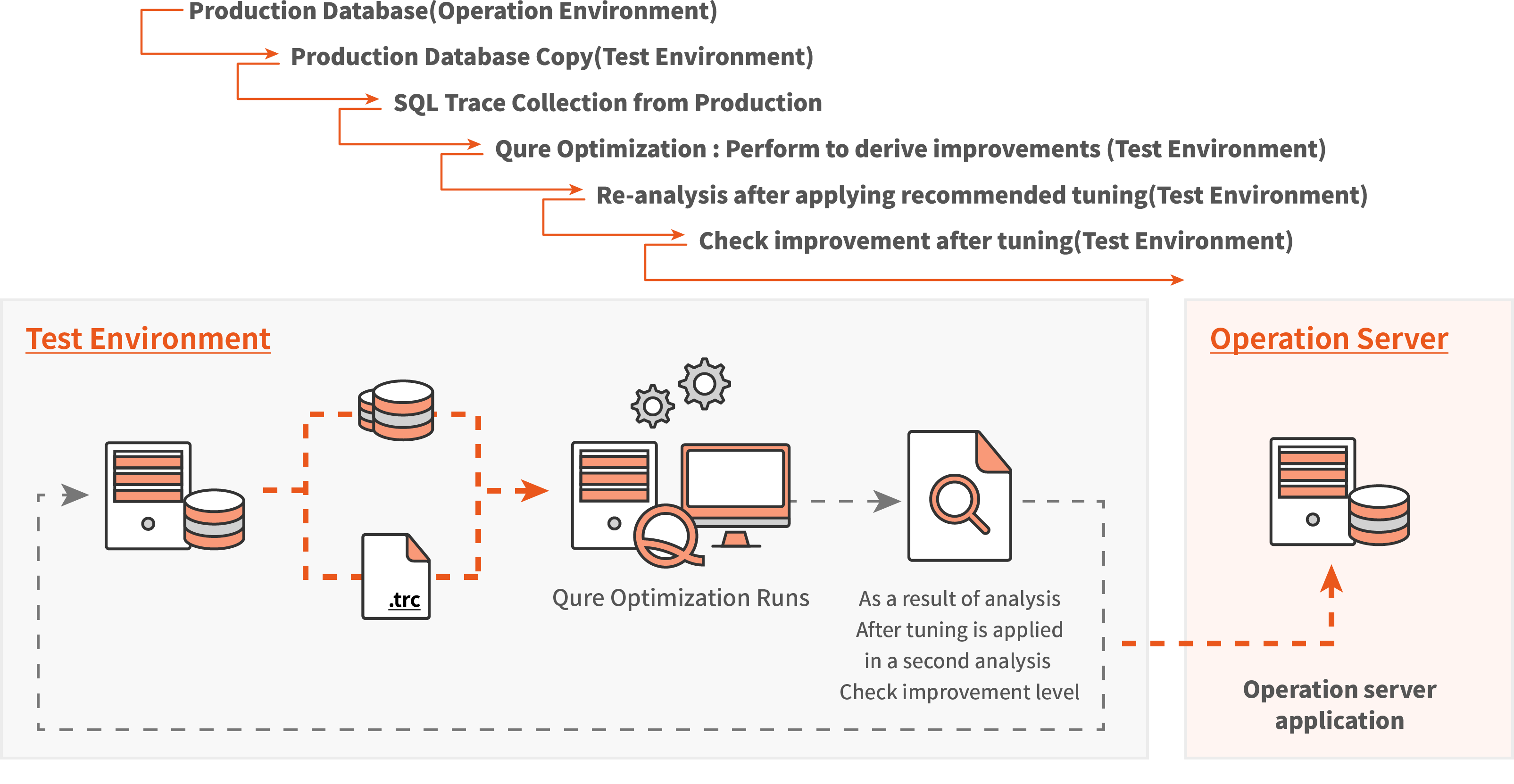
2. Experda
– Founded in 2007, Jerusalem, Israel
– Focus on speeding up applications using SQL Server (only “Workload tuning”)
– Amy Levin (CTO), a leading SQL Server Expert and Microsoft MVP
– Various global references
- Only some malicious Qurey(Query by Query)
- An additional speed problem occurs after a scheduled time – not suggesting a fundamental solution
- Since it is not possible to analyze the overall correlation with the target (index, batch, and query), only highly tuned experts can tune it in a limited way.
- Time and expense are repeated and continuously invested
I. Problems with Existing Methods (Query-by-Query Tuning)
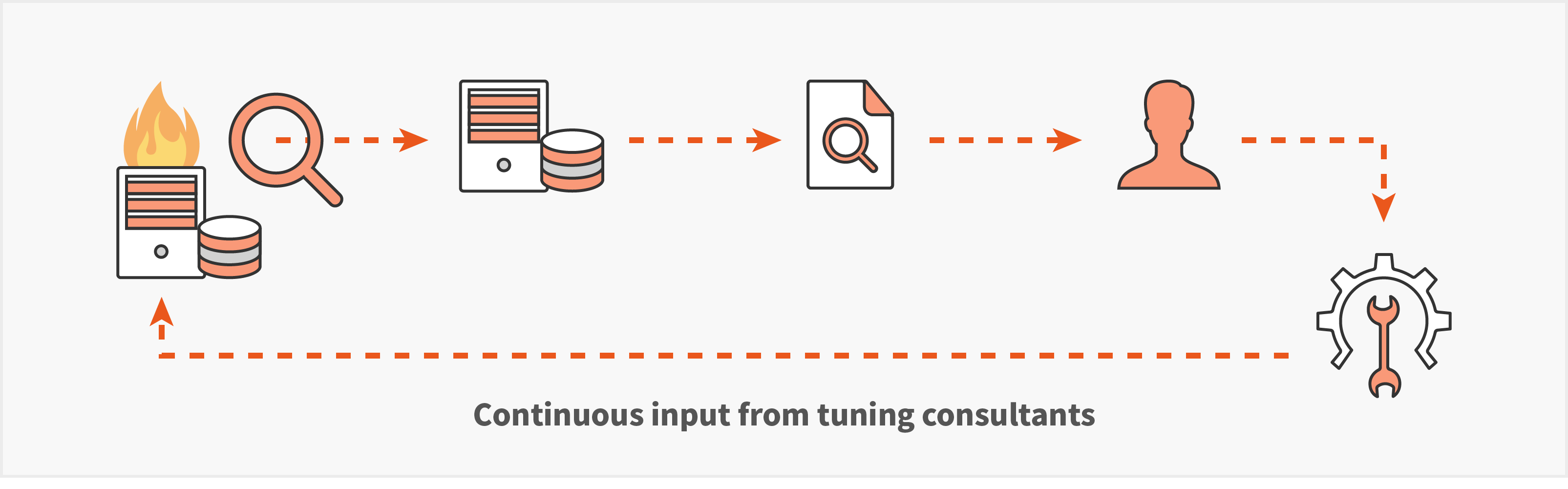
II. How Data Optimizer Tunes Workloads
- Advanced impact of each recommendation (CPU, memory, IO, etc.)
- Provide a guide to modify and rewrite the SQL query
- Guides for changing indexing schemas are provided
- Provide other Query and Batch information related to schema changes
- Detailed analysis of potential deceleration factors
- Others…
- Apply scripts (automatically apply recommendations)
- Revert scripts (automatically applied recommendation recovery function)
III. Providing Recommendations for Speed Improvement
Provides a complete guide to optimal speed
Recommendations / Apply to Production DB (optional)

 view
view view
view view
view view
view view
view view
view view
view view
view view
view view
view view
view view
view view
view view
view view
view view
view view
view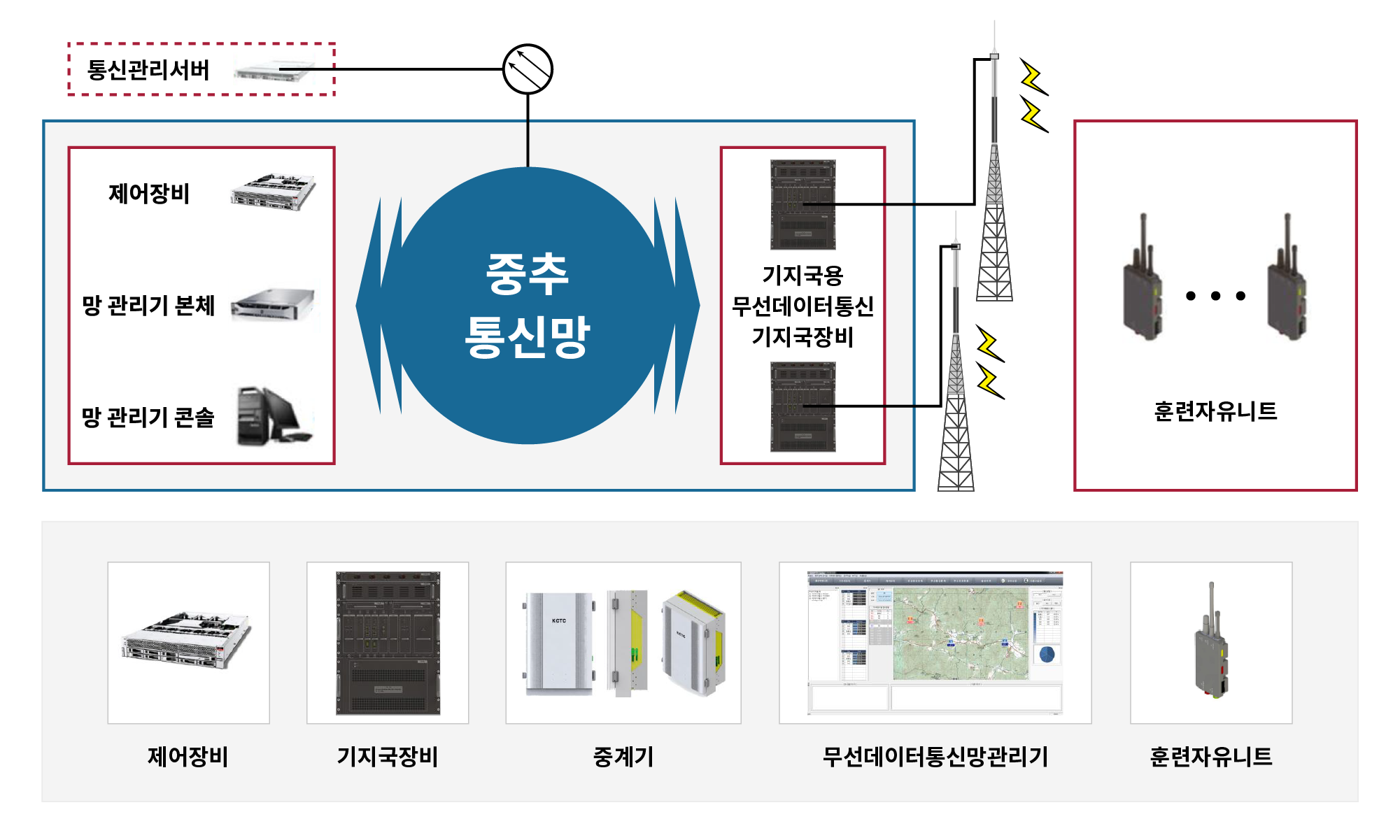

 제어장비
제어장비 기지국장비
기지국장비 무선데이터 통신망관리기
무선데이터 통신망관리기 중계기
중계기 훈련자유니트
훈련자유니트 레이저 발사기
레이저 발사기 훈련자 감지기
훈련자 감지기 기지국
기지국 중계기
중계기 안테나
안테나 PU(단말)
PU(단말) 전투조끼
전투조끼 발사기
발사기 감지단자
감지단자 전시창
전시창 리모컨
리모컨 훈련자 유니트
훈련자 유니트 전자탄창
전자탄창 훈련정보 수집기
훈련정보 수집기 훈련전송 수집전송용 SW
훈련전송 수집전송용 SW 전광판
전광판 view
view view
view view
view view
view